![]() Out of the box your connection to node-red is insecure.
Out of the box your connection to node-red is insecure.
If you are exposing node-red to the Internet or just want a more secure installation then you can:
- Enforce an SSL connection.
- Require Username and Password Authentication
Note:
When configuring multiple security settings I try to configure one security setting at a time and test it before configuring the next.
Configuring SSL
To do that you will need to install a certificate and key on your node-red server.
In this tutorial we will be using a self signed certificate which we will create ourselves using openssl and I will be using raspberry pi to host node red.
Creating a Self Signed Certificate
1.Create a private key
openssl genrsa -out node-key.pem 2048
2. Create a certificate Request
openssl req -new -sha256 -key node-key.pem -out node-csr.pem
You will need to fill out a form the most important entry is near the end and is the common name field.
This should be the FQDN of the server hosting nod-red or the IP address. I used raspberrypi.home
3. Sign the Certificate with the Private key to create a self signed Certificate
openssl x509 -req -in node-csr.pem -signkey node-key.pem -out node-cert.pem
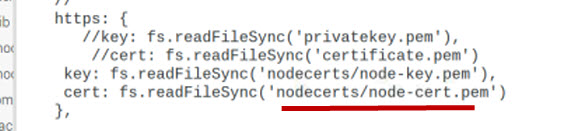
Note: I created my files in sub folder of my .node-red folder called nodecerts.
Editing the Node-Red Settings File
I recommend you use your own settings file while you are trying this. You can copy the settings file to the default location when you have tested the configuration.
The default settings file is called settings.js located in /usr/lib/node-modules/node-red/ folder by default. (Raspberry pi).
I copied this to my .node-red folder and renamed it mysettings.js.
You need to do the following:
un-comment the line
var fs=require("fs")
Which is near the top of the file.
In the AdminAuth section un-comment the https section and edit as shown in the screenshot below:
There is another setting
requireHttps: true,
Note: there should be a comma at the end
This should cause a redirect to https if you try connecting to http.
Note:I didn’t get this to work with SSL so you may need to skip this.
You can now start node-red using:
node-red -s mysettings.js
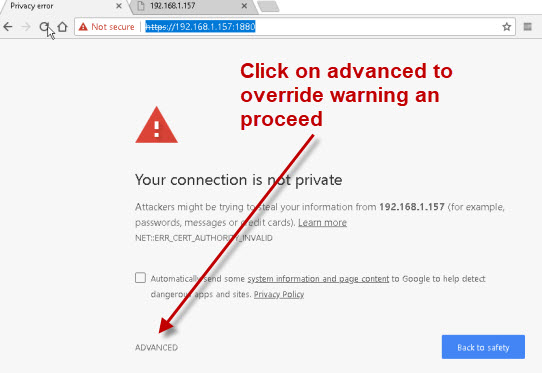
Now when you connect using the browser you should get a certificate warning which you can override.
Username and Password Authentication
The Node-Red Editor and Admin API support two types of authentication:
- username/password credential based authentication
- OAuth/OpenID authentication -since Node-RED 0.17:
On node-red there are three places were you can configure/require authentication.
- The Admin console- Node red editor
- Nodes
- Static Pages
In this section we will look at username and password authentication for the admin console.
The default settings file has a section called Securing node red which is commented out and serves as a template.
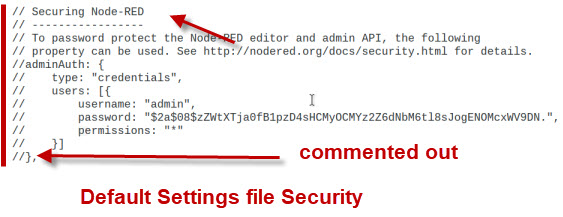
The default entry shows the userAdmin with a password of password (hashed) and all permissions (* wildcard).
You can create additional users by copying the users section and editing accordingly.
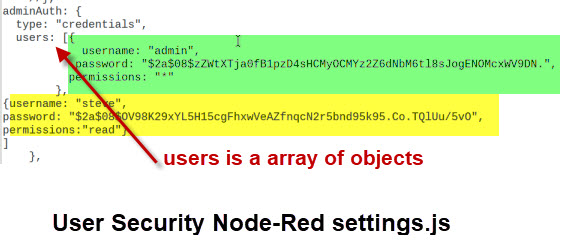
Note: The password hash for steve is different than that of admin,but the actual password is the same. This is how the bcrypt algorithm works
Steve has got read permissions which means that he cannot edit or create new flows.
Generating Passwords
You can create passwords for use in the settings file by using the admin command line hash-pw command as follows:
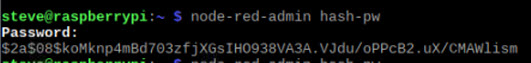
If you right click on the password you can copy it using CRT+C.
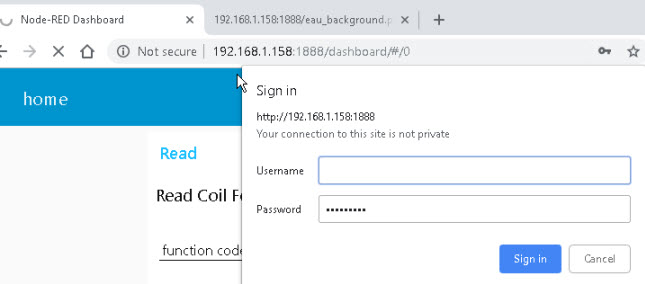
When you try to connect to the admin page you should get a login screen.

You can also use online bcrypt tools for creating the passwords like this one.
Securing The Dashboard
To secure the node-red dashboard use the httpNodeAuth setting.
Only a single user account is allowed.
httpNodeAuth: {user:"fred",pass:"$2a$04$3gkGX/Q4VZ//F37kWvSU9eE9EM1WO2rdWk1oj/kfXIbeBON5eA56S"},
You create the passwords using the hash-pw command line tools as before.
When you try and access the page you should be prompted to login.
Securing Static Pages
Node-red can serve static web pages. These web pages are served from the usr/lib/node-modules/public folder by default.
You can change to location by using the httpStatic setting in the settings file.
Generally you would want to move it to a folder in your home directory e.g.
httpStatic ‘/home/steve/.node-red/node-red-static/’
You can secure this folder using the httpStaticAuth setting.
httpStaticAuth:{user:"fred",pass:"$2a$04$3gkGX/Q4VZ//F37kWvSU9eE9EM1WO2rdWk1oj/kfXIbeBON5eA56S"},
You create the passwords using the hash-pw command line tools as before.
When you try to access the page you should be prompted to login.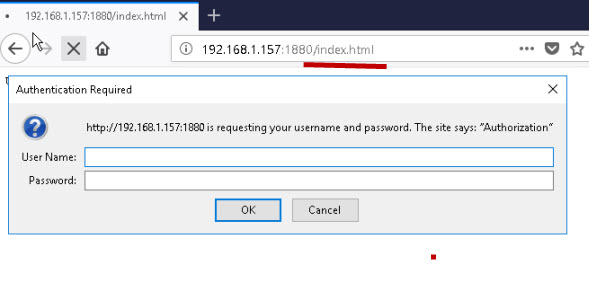
Note: Only a single account is possible. It also appears to clash with the httpNodeAuth setting which is used to secure the dashboard.
If using both use the same username and password for both.
Summary
On a working system tightening the security on your node-red installation is important.
Requiring username/password authentication and SSL is a minimum requirement. See Exposing Node-Red to the Internet
Resources and Related Tutorials
- Node.js Documentation – Instructions for creating self signed certificate for node.js.
- Online bcrypt password generator
- Node-Red Settings.js File – Node-Red Admin
- SSL and Certificates Explained
- Certificates and Encodings
- Configuring The MQTT publish Node
Hello. Is there a way to configure Node-Red with SSL only with the server certificate? I would like to connect a PC to an MQTT broker in the cloud. But I only have the cloud server certificate.
Sorry confused by the question. Not sure what MQTT has to do with it.Are you securing node-red or MQTT. Where is node-red located local or cloud.?
Rgds
steve
I have an IOT monitoring device that sends data to an MQTT server in the cloud with SSL (Hivemq Broker Cloud). I want the information that reaches the server in the cloud to go to Node-Red which will be in another network.
I want this system to be fully secure with SSL. I have already configured the connection of the device with the server. Now I need to configure the server connection to Node-Red with SSL.
I did some research, and found that I can connect the server with Node-Red with SSL without uploading a file with certificates and keys. I just need to enable port 8883 and secure connection on Node-Red.
I’m just wondering if it’s safe to do this with Node-Red over http.
Thank you for your attention.
The way you describe it node red will be getting data from the mqtt sever over MQTT not http and all you need on node red is the ca certificate you use on the mqtt broker.
Does that make sense or have I misunderstood.
Rgds
Steve
OK. Thank you very much for your attention!
Steve, I enjoy your articles. Similar to Andre, I run an IOT setup with a RasPi running Node-Red as well as MQTT local broker. SSL – TLS gets over my head pretty quickly, but I did manage to get SSL/TLS/CA security set up on my local Mosquitto Broker using LetsEncrypt and my MQTT broker is accessible via the internet via my Domain name. I do not have any (that I know of) WAN access to my local Node-Red server and don’t really need to. But do want to limit its exposure. Can you expand on your last comment to Andre?
“The way you describe it node red will be getting data from the mqtt sever over MQTT not http and all you need on node red is the ca certificate you use on the mqtt broker.”
Correct.
You would only need ssl on node-red if you want it to be accessible from the Internet.
If you run nodered on the same machine as the mosquitto broker then you could use the same certificate to secure node-red if you wanted to.
Does that make sense?
rgds
Steve
So, if my MQTT config has something like these 2 lines in it:
certfile /etc/letsencrypt/live/domain-name/fullchain.pem
keyfile /etc/letsencrypt/live/domain-name/privkey.pem
Then in Node-Red “settings.js” I would put:
https: {
key: require(“fs”).readFileSync(‘/etc/letsencrypt/live/domain-name/privkey.pem’),
cert: require(“fs”).readFileSync(‘/etc/letsencrypt/live/domain-name/fullchain.pem’)
},
Unless directory and/or file “permissions” get tangles up – then I guess I would have to copy the 2 pem files to a folder that Node-Red has access to? I will do a bit of testing. Thank you!
Hi Steve! I successfully create the certificate, integrate it with node-red setting and also included the certificate on the browser of another devices that is trying to access it.
The page successfully loaded as https and I can access it but for some reason the browser keep telling me
the site is not safe. I wonder what went wrong. Is this happen because the wrong FQDN (or something else)?
The node-red address is https://192.168.1.189:3001
I wrote that as the FQDN but my browser keep rejecting the certificate.
The common name you used on the certificate should match the url you use.
If the common name you used was the IP address then you need to use the IP address to access it.
Can you remember what you used?
Rgds
Steve
Hi Steve, thanks for the tutorial. I have made all the steps and able up until https “the site is not safe, click advance to..” same as Kamil’s and I understood your reply to Kamil’s on common name or ip on the certificate. But I cant see you insert any domain name while generating the SSL certificate. Where should I fill up my domain name?
Btw, I deployed node-red at hosting server. my main page already secured by using Let’sEncrypt. Only node-red I unable to secure.
It is the the common name field. When creating the certificate you are asked several questions like organisation etc. It also asks for common name which should be the IP address or domain name of the machine hosting node-red.
Rgds
Steve
Hi Steve
I wanted to secure my flow by enabling https using static object. My node-red flow is running on my Windows laptop. I have created “nred.key” and “nred.crt” using openSSL in the .node-red folder.
Now I am defining the static object as follows
https: {
key: require(“fs”).readFileSync(‘C:\Users\jayant\.node-red\server.key’),
cert: require(“fs”).readFileSync(‘C:\Users\jayant\.node-red\server.crt’)
}
But I am getting the following error
Error loading settings file: C:\Users\jayant\.node-red\settings.js
Error: ENOENT: no such file or directory, open ‘C:Usersjayant.node-redserver.key’
errno: -4058,
syscall: ‘open’,
code: ‘ENOENT’,
path: ‘C:Usersjayant.node-redserver.key’
Please help me out defining the path correctly or if anything else that I can do.
Regards
Jayant Kaushik
Just specify the files relative to the .node-red folder. The lines
key: require(“fs”).readFileSync(‘C:\Users\jayant\.node-red\server.key’),
cert: require(“fs”).readFileSync(‘C:\Users\jayant\.node-red\server.crt’)
don’t look like the lines in the tutorial where did you get them from?
I haven’t done it on windows but if you are still having problems let me know and I will try it.
rgds
steve
Hello Steve, is it possible if you could try it on windows?
I created the SSL certificates perfectly well but when I tried to launch node-red I have the same problem as Jayant Kaushik.
I think there is a problem with the directory we both define in:
key: require(“fs”).readFileSync(‘C:\Users\username\.node-red\SSL_cert\nd_key.key’),
cert: require(“fs”).readFileSync(‘C:\Users\username\.node-red\SSL_cert\nd_cert.crt’)
Thank you very much!
Regards
Hi Steve
Thanks for your reply. But I have tried mentioning the same key and cert files correctly, created using openssl. But still no luck as Emiliano.
Request you to please try it on Windows.
Regards
Jayant Kaushik
Hi Steve,
Is it necessary to use the algorithm SHA-256 or could we use another one?
Thanks,
María
Good question. I’m afraid I don’t know. I would assume no but the other end would need to know the algorithm. Not sure if it is passed in the protocol. Something I will need to look at in more detail.
Rgds
Steve
Hi Steve,
All Unix commands have worked correctly.
On the Mac the settings file is in /usr/local/lib/node-modules/node-red/ not in /usr/lib/node-modules/node-red/. But this is not the one to be modified.
There is a hidden folder at user level, /Users/carles/. node-red/, which is where the Manage palette places the modules we import and also has a settings file. This is the one that needs to be changed, you must also put there the folder nodecerts
Regards,
Carles
Tks for that
Rgds
Steve
Hi Steve,
I started using Node-Red and searching the internet I found your blog. You always refer to Windows and Linux but not to MacOs, this tutorial and the others could be useful for MacOs?
Thanks for your time,
Carles
Hi
It’s just because I don’t use a Mac but it should all work ok on Mac as it is nodejs.
Rgds
Steve
Thanks for the answer Steve. Node-Red works perfectly on a Mac, what I meant to say was if the commands you use on Linux are equivalent to Mac Unix. I would like to use the commands in this blog, but I’m not sure if they are compatible.
Excuse my English if something is not well understood, all credit goes to DeepL translator
Regards,
Carles
Not sure either but I would expect them to be the same as they are node-red related and not OS related. Just try them and let me know.
Rgds
Steve
Hi Steve, been using this security for a while now with no problems. Yesterday I moved the microSD card from my Pi4 to a Pi Zero and the Alexa node wont work. Its got a static IP address so no change when moving from one device to another. Is the SSL key specific to the machine it is set up on? Do I have to create another key?
Kind regards
Don…
It specific to the name. Did you name it the same as the old pi?
Hi Steve and thanks for your reply. I cloned the microSD card to my pc as backup and then inserted the card from the P4 to the P0. So, nothing was changed. In the mean time I have started from fresh so I can sue it on Buster and its all working. So I start to add the OpenSSL to the fresh install with the first command: openssl genrsa -out node-key.pem 2048 and get the following error:
pi@raspberrypi:~ $ openssl genrsa -out node-key.pem 2048
Generating RSA private key, 2048 bit long modulus (2 primes)
………………………….+++++
………….+++++
e is 65537 (0x010001)
Can you help with this please.
Thanks Don….
Hi
You are missing -des3
rgds
steve
Hi, could you please give a bit more info as I’m not sure where to enter the -des3. Could you type the full command line as it might also be helpful for others. Many thanks Don….
openssl genrsa -des3 -out node-key.pem 2048
good tutorial.
I found that I needed to use __dirname before the path to the key and certificate.
eg.
https: {
key: fs.readFileSync(__dirname + ‘/nodecerts/node-key.pem’),
cert: fs.readFileSync(__dirname + ‘/nodecerts/node-cert.pem’)
},
Hi Steve
First of all, congratulations on this tutorial and on everyone you have on your website, they are absolutely impressive.
I have had problems configuring the SSL protocol by this method and once configured, I have accessed from Chrome with the security warning but all the time it puts in Node-RED Lost connection to server, reconnecting in XXs. Try now
Any ideas? Thank you
Hi
I seem to remember I had a problem with chrome some time ago with the connection dropping. Have you tried another browser?
In addition are you going through a proxy or similar as the connections uses websockets.
rgds
steve
Hello Steve,
thank you for the great tutorial. After setup ssl, i opend the editor. I get a „connection lost“ message after a second. Clearing the cache of the browser didnt solve this.
Any idea?
Meik
Did you get any warning about insecure connection?
Rgds
Steve
Thanks for your post.
Hi again Steve,
Fantastic tutorial and now I have id and password set up on node red and dashboard. I have followed your tutorial to the letter but am confused over the SSL certs. When I logon with my chrome brower using https it still says not secure and i have to click on the advance button to access my website. Is there anything more I need to do to get SSL working correctly.
Cheers Don…
Don
No that is normal as you are using a self signed cert and the browser doesn’t know about it. If you add it to your certs it will get rid of the error message but if you access it from a browser on another computer it will appear again. It is nothing to worry about it us still using SSL.
Rgds
Steve
Hi Steve,
How to add it to my chrome? i tried to import the pem file but chrome is not recognizing.
Can you use the ask steve page and send me the error message and the pem file
Rgds
Steve
Is there any way to remove the error message?
Do you mean the warning message about the certificate. If so then there should be an option to add it to your trusted store and that will remove it.
Rgds
Steve
Hi, will this let me access nodered dashboard across the internet safely. Many thanks…
Hi,
Thanks for the instructions. No login window appears when I try to access either the editor interface of the ui. For the editor I just get the message that the site can’t be reached. I can access the ui, it is read-only. there is no promt for user or password anywhere. Do you have any ideas?
Thanks
Try closing and opening the browser.
If no joy send me your setting file using the ask-steve page and I’ll take a look. When you do let me know the password so I can check.
Rgds
Steve
hi, i am using httpNodeAuth but once i login there is no logout button or something like that, and i must change the password or user if i want to login again, why?, thanks
Hi
Hadn’t really noticed until you mentioned it. The login is a security feature that probably not many people currently us as most implementations are Internal.
I’ll try to find time to explore it again to see if there are other options available.
Hello Steve,
thanks for this awesome guide.
Do you know how to setup a proxy config for node-red? I only read something about using environment variables, i defined them but it still won’t work.
HTTP_PROXY -> HTTP_PROXY=http://url
HTTPS_PROXY -> HTTPS_PROXY=http://url
im using node-red with IBM Watson Assistant (conversation) and the request fails because of the proxy.
error message of the node-red server:
[error] [watson-conversation-v1:chatbot] Error: tunneling socket could not be established, cause=connect ECONNREFUSED 127.0.0.1:80
Hi
When I did it I used a nginx server and it involves zero change on node-red.
I had never use nginx and it was pretty straightforward. I can send you my nginx config file if you want just use the ask steve page.
rgds
steve
Hi Steve,
Very good how to made here. May I ask for your reverse proxy example too?
Thanks
Daryl
This is the code I used on the nginx server. I’ve change the port numbers the code is for two connections. Mode red is running on 192.168.1.21. Outside access is on the external Ip address port 38111 or 38112. I used no-ip to get a domain name.
It also uses ssl which you can see in the code.
I’m not a nginx expert I put it together from nginx examples and trial and error.
rgds
Steve
server {
listen 38112 ssl;
server_name steve-laptop;
ssl_certificate /home/steve/ssl/server.crt;
ssl_certificate_key /home/steve/ssl/server.key;
proxy_redirect off;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header host $http_host;
proxy_set_header Upgrade $http_upgrade;
proxy_http_version 1.1;
proxy_set_header Connection “upgrade”;
location / {
proxy_pass http://192.168.1.20:1880;
}
}
server {
listen 38111 ssl;
server_name steve-laptop;
ssl_certificate /home/steve/ssl/server.crt;
ssl_certificate_key /home/steve/ssl/server.key;
proxy_redirect off;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header host $http_host;
proxy_set_header Upgrade $http_upgrade;
proxy_http_version 1.1;
proxy_set_header Connection “upgrade”;
location / {
proxy_pass http://192.168.1.21:1880;
}
}
I have followed this link.
But when i am sending webhooks from shopify to node-red http end point . It is not sending any request then i have trued beeceptor and redirect request to my node-red end point there it is throwing below error-
SSL or certificate issue while connecting.
I have purchased SSL also for a domain and redirected that to my node-red IP but still the same issue is there.
Am I correct in understanding you trying to connect shopify site to node-red?
Can you access node-red with a normal browser?
rgds
Steve
HI is there way for /ui to be secured without popout window but to enter credentials like on login screen, actual page?
Not as I know
Rgds
Steve
How would I do this within a container?
Sorry But I don’t use containers at the moment
rgds
steve
Can I make the dashboard only open on local PC? Basically disabling web access.
Not with the node-red settings. On Linux you can use iptables to do what you want on Windows you would need to use the windows firewall.
Hi Steve,
I could install everything as discribed. Thank you for the guidens.
Where I do have a problem is when I call with the browser chrom or firefox my node-red with https://xxxx.xxx:1880, I still get an unsave connection. It looks like they allow not anymore self signed Certificates.
Is there a way to extend the self signed Certificate to fulfill the requested certificates by the browser chrom? I could not find anything on the internet regarding this.
If I take the browser Edge, then it works well with a save connection to my node-red. It seems that Edge is not testing what other browsers now do.
Thanks, Bruno
I know Chrome has tightened up on SSL certificates but I would assume that it still allows access but with a warning. Is that what you are seeing?
Hi Steve,
is there a way to create more than one user for the httpStaticAuth settings?
Thanks,
Tobi
No not as I know.