There are three main ways of obtaining SSL certificates but purchasing a commercial certificate from a provider is probably the most popular option.
When you do this you will be provided with a collection of files.
In this tutorial we look at using the certificates provided by Thawte to configure a mosquitto broker to use SSL.
We will be configuring the broker to support MQTT+SSL and also MQTT+websockets +SSL
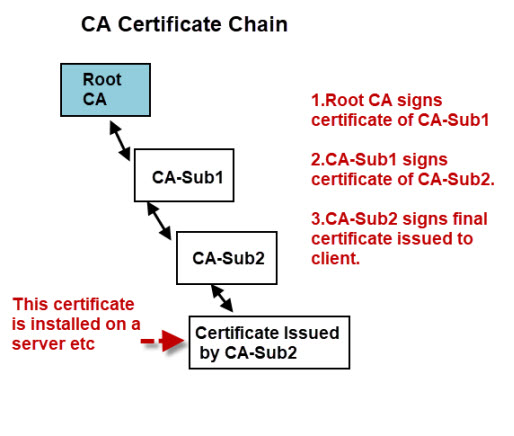
Commercial certificates usually have a Root CA+Intermediate certificate+broker or server certificate in a certificate chain.
Generally the CA is part of your trusted store and if you are using these certificates with a web browser then there is usually not problem.
However if you are accessing the broker using a python client for example then you will need to provide the root CA.
In addition you may also need to provide the intermediate CA certificates.
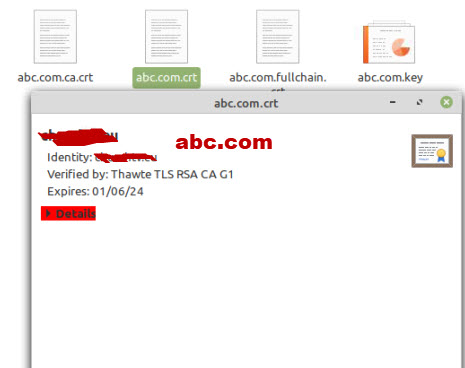
When you purchase your certificate you are usually provided with a zip file containing your files.
An example is shown below:
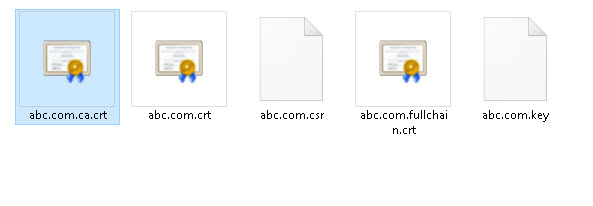
You should note that the domain name that you will be using is usually part of the file name but to protect privacy I have renamed these to abc.com.
In addition the files were provided with a .pem file extension and so abc.com.crt was in fact abc.com.crt.pem.
You can leave it but I removed it as on Windows .pem files are opened with notepad, whereas .crt files are opened with the certificate tool which is very convenient.
.pem files are text based and easier to work with and I think most providers provide these file types, but if you have .DER certificates then there are tools to convert them. See this tutorial – DER vs. CRT vs. CER vs. PEM Certificates.
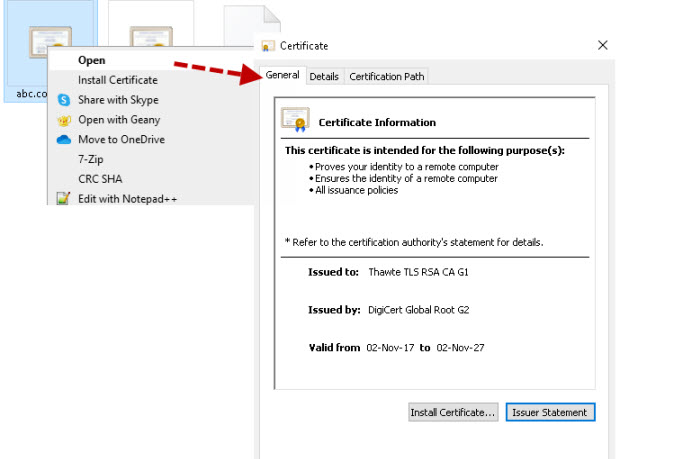
Below is a screen shot of a file .crt opened on windows:
On Linux you can select the open with view File option and you will see:
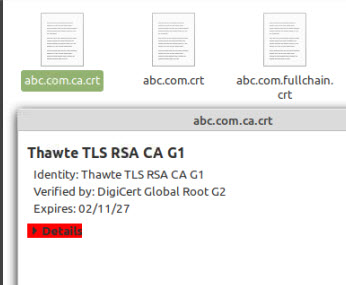
If you look at the above screen shot you will see that the certificate is an Intermediate certificate and signed by the root certificate (DigiCert Global Root G2).
If we look at the server certificate shown below
Then we see it is signed by the Intermediate certificate Thawte TLS RSA CA G1.
So we have our certificate chain root>intermediate>server
The last certificate supplied is the fullchain certificate.
This is actually 2 certificates the server +intermediate as shown below:
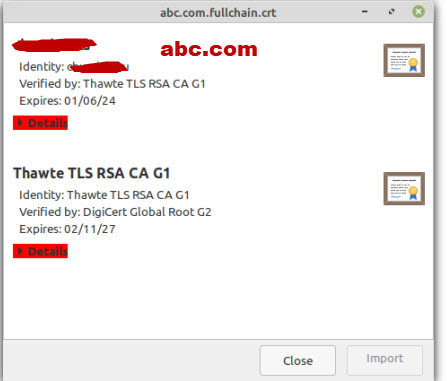
Now for it to work we need all three certificates but we are missing the global root.
Now this isn’t a problem if the client is a web browser but in my case it is was a python client and, so I needed a copy of the root CA.
So a quick search and I found it on the Digicert website
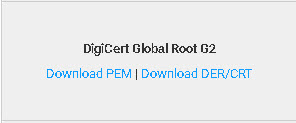
So I simply downloaded the .pem version and changed the extension to .crt and the name to simply root.crt.

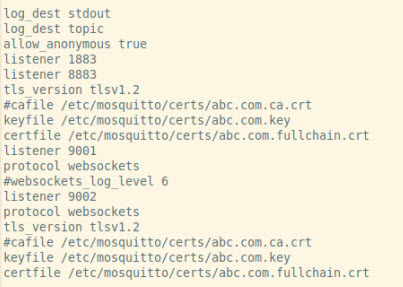
Broker and Client Configuration
On the broker I use the fullchain +server key.Also notice the cafile is not used as this is only required when using client certificates.
Python Client
I need to add a tls entry as shown
client.tls_set('c:/python34/steve/mqtt-demos/certs/root.crt',tls_version=2)
On the Python client I need to use the Root certificate that I downloaded.
Web Browser Clients
No configuration should be necessary as the root certificate should already be in the trusted.certificate store.
Common Problems
The most common problem that I have seen is a missing certificate in a certificate chain and it is usually an intermediate certificate
In addition because root commercial certificates and part of the browser and most provides provide certificates for use on a web server then they don’t include the root CA in the chain and so you often need to download it.
You can also use the root CA bundle which also works in place of the individual root CA. You can download this bundle here
If you are running Linux then you can copy the file from /etc/ssl/certs/ca-certificates.crt.
Resources and related tutorials:
- How certificate chains work
- Extracting certificates and keys from a pfx file
- Windows where is my private key
- SSL and SSL Certificates Explained For Beginners
- Using A Lets Encrypt Certificate on Mosquitto
- Mosquitto MQTT Broker SSL Configuration Using Own Certificates
